SSL Decryption: Benefits, Challenges, and Best Practices

Corporate networks are experiencing ever-growing traffic — both in and out. Enterprises have the burden of not only handling large traffic volumes but ensuring quality traffic that travels bilaterally.
Among the many strategies and technologies adopted, SSL is considered a basic but essential security practice. Understanding SSL decryption — including the concept, benefits, drawbacks, and best practices for how to use it — are a key component of navigating Palo Alto. Read on for more information about SSL encryption and deployment challenges, and if you’re ready to learn more about how to manage Palo Alto next generation security platform and architecture, check out the PCNSA online training course from Keith Barker.
What is SSL Encryption?
To better understand SSL decryption, we need to know about the encryption side because encryption and decryption exist together. SSL stands for Secure Sockets Layer. It is an encryption-based internet protocol that allows authenticated and encrypted links between networked computers.
The protocol was first invented by Netscape in 1995 with the aim of ensuring privacy, authentication, and data integrity in internet communications. Today, we use modern TLS encryption instead of SSL, but the related technologies are still referred to as "SSL" or "SSL/TLS." When a website uses SSL/TLS, it has HTTPS and when it doesn't, a website has HTTP.
Why is it Important to Inspect SSL Traffic?
SSL encryption was designed to securely deliver traffic over the internet. As all data is encrypted, any malicious third party cannot intervene and read the content. However, as normal traffic can be encrypted, so can malign traffic. This created the necessity for examining SSL traffic to filter out that risky traffic.
This activity involves, first, intercepting the inbound encrypted traffic by the interceptor and decrypting the traffic, second, inspecting the content, and third, encrypting the traffic back and sending it to the destination. With this SSL inspection activity, companies can fend off their digital assets from ill-intended traffic.
How to Know if a Site has an SSL?
Now that we know the concept and the importance of SSL, our next question would be, "How we can identify that a website uses SSL?" The easiest clue is whether the URL address starts with "https". HTTPS, or Hypertext Transfer Protocol Secure, indicates the name of the protocol and the last character, "s", tells you that the website uses an SSL certificate.
For example, if you use Chrome, check the lock icon in your URL address section. When you click the lock and click "Connection is secure", it displays connection details including the validity of the certification.
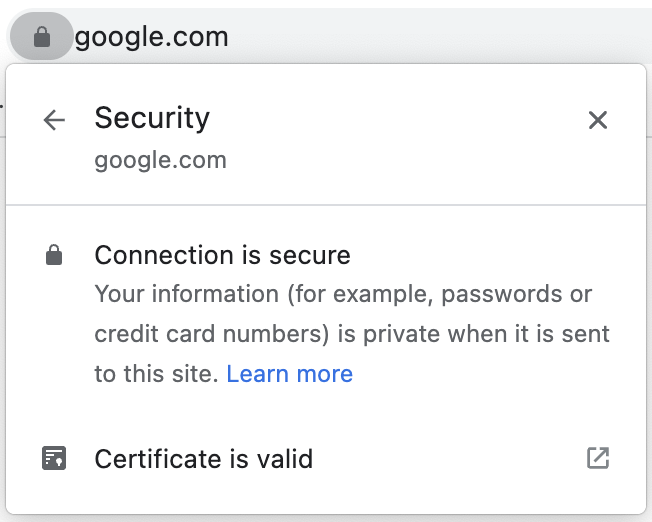
Checking SSL certificate
Most modern browsers have this feature, so checking the address and certification information can be a good practice. When you access major websites, even if you type the http address, you would be directed to https automatically for your and their security.
What About the Privacy Implications of Inspecting SSL Traffic?
A discussion that's worth having is the conflict between inspecting SSL traffic for security and accessing private information that's encrypted in normal traffic. Is it justifiable to look into sensitive private data for the sake of corporate digital assets? However, we need to consider the potential risks of not inspecting SSL traffic because of the privacy implications.
Without the inspection, an enterprise cannot protect users and corporate assets from threats. When companies fail to inspect traffic, this can lead to even broader issues than privacy concerns. Without the means to intercept SSL traffic, a firm cannot effectively prevent sensitive data leakage and protect end-user data.
This does not mean that companies can simply assume that they can examine private data without informing end users. They need to take some time to explain why they perform an SSL/TLS inspection and this should be situated as part of the user policy for their website. It will be desirable to review such policy with relevant parties such as legal entities and external advisors and also consider regional compliance like GDPR.
Why is SSL Decryption Important?
To inspect encrypted traffic, it is required to decrypt SSL. With encryption, people cannot view the contents of the traffic. Nowadays, hackers and ill-minded beings take advantage of this secrecy and insert malicious code to manipulate the target system and intercept important data. This creates a circumstance where the receiving end cannot trust all incoming traffic.
To filter out risky traffic, companies should decrypt the data to check the content. This SSL decryption activity allows unveiling encrypted traffic and inspecting what's inside. After inspection, the traffic is then encrypted back again and sent to the destination.
The use of SSL decryption has become more important due to the increased volume of encrypted traffic. There are two main factors that drive that increase. The first reason is Google. In 2018, Google started flagging websites without SSL encryption. For example, in a Chrome browser, a red flag will display next to the URL. Also, Google factors this when it decides a Google search result. When everything is the same but one website has SSL and the other doesn't, the one without SSL is likely to be ranked lower in the Google search result.
The next reason is due to increased awareness of security. Across the globe, countries applied security laws to protect their people online. This global movement encouraged enterprises to adopt SSL encryption to abide by the law and protect their users.
What are the Challenges of Deploying SSL Decryption?
When you start planning to deploy SSL decryption, you can face challenges due to technical and circumstantial difficulties. We can categorize the challenges into these three:
Complex decryption architecture. There are numerous tools and methodologies with different security goals. Some of them are designed for SSL decryption and traffic inspection and the rest have different use cases. Companies need to take care of different aspects of security, which makes them use a mixture of tools. Amid these, it can be a challenge to implement SSL decryption while maintaining the performance of the rest of the security tools. A failure to do this can create a bottleneck or a loss of traffic.
Decryption performance. Traffic decryption and encryption can consume a lot of computational resources. When companies experience this burden, sometimes they select some of the traffic for inspection. Also, traffic volume changes throughout the day, week, month, and year. Allocating the right resources considering this seasonality can be also a challenge. When you can optimize the performance, this can also have a positive impact on cost.
Security regulations. Each state and country can have different regulations that stipulate lawful decryption practices. Implementing SSL decryption without proper legal knowledge can lead to privacy violations. Because of this, it can be challenging to strike a balance between following the regulations and ensuring safe traffic.
SSL Decryption Best Practices
Understanding the challenges, we need to build strategies and implementation plans to prevent poor design. When we enable decryption, this can affect the user experience in your websites and systems. Thus, planning, testing, and education are important for successful implementation.
Expand decryption coverage
When you plan how much traffic you want to decrypt, it is desirable to maximize the decryption rate for those that are not private and that is sensitive. To set the coverage goal, you need to consider your resources. When your decryption rate surpasses the capacity, it can lead to latency and dead traffic. Also, you need to consider and follow the regional laws that regulate traffic decryption and user notification.
Measure performance before and after deployment
By comparing available resources in your firewall before and after decryption deployment, you can estimate how much resource is consumed for how much traffic. Using this estimation, you can calculate the required firewall resources for your targeted decryption rate. You can perform this measurement in your test or stage environment.
Stage and prioritize deployment
Before deployment to production, it can be a good practice to select teams that are willing to accept decryption. Then, after your testing, instead of deploying for the entire organization, limiting that functionality to selected teams can be a good learning opportunity. You can use this to measure resource usage such as CPU and memory in the firewall for validating your initial estimation and improving it. As you measure the performance and go through the full deployment cycle, you can familiarize yourself with the process and minimize potential mistakes during full-fledged deployment for the entire organization.
So Just Exactly How Important is SSL Decryption?
Understanding and implementing SSL encryption and decryption is an important part of any organization’s security initiatives. Knowing how to deal with the challenges for decryption deployment — including having a better understanding about SSL decryption from the various angles mentioned above — will help you to plan wisely for SSL implementation and minimize the chance of failure. It’s safe to say that the use of SSL will only grow in the future because of Google’s policies and raising awareness of security.
delivered to your inbox.
By submitting this form you agree to receive marketing emails from CBT Nuggets and that you have read, understood and are able to consent to our privacy policy.