What is a Distributed Denial-of-Service (DDoS) Attack?

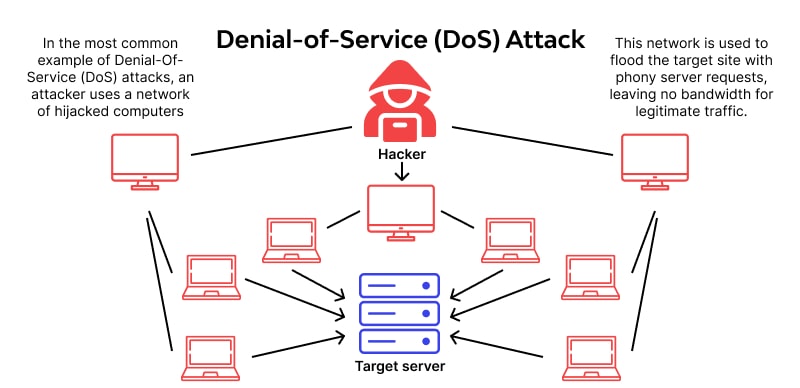
Quick Definition: Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) attacks exploit vulnerable services and systems by overwhelming a target with more traffic than it can handle, making websites, servers, or networks unavailable to users.
A DoS attack typically comes from a single source. A DDoS attack, on the other hand, is carried out by multiple compromised devices (often part of a botnet) flooding the target simultaneously, making it harder to block and far more disruptive.
Picture this: you’re at home cooking, and something spills over on the stove. At the same time, someone rings your doorbell, so your dog starts barking. Wouldn’t you know it, your phone starts ringing, too. There’s too much chaos happening at the same time, and you can’t respond to it all at once, so you freeze up.
If you’ve ever experienced a situation like this where you’ve been overwhelmed as a response to multiple things simultaneously demanding your attention, you've experienced the human equivalent of a Denial-of-Service (DoS) attack.
In this article, you will learn about the different types of Denial-of-Service attacks, how they occur, how to help protect against them, and their impacts.
3 Varieties of Denial-of-Service (DoS) Attacks
Denial-of-service attacks (DoS) are attacks aimed at disrupting services by overwhelming resources. Malicious actors use DoS attacks to prevent users from accessing specific resources, like websites. They come in three varieties: volumetric, protocol, and application-layer attacks.
Volumetric attacks are just that; they are designed to disrupt services by overwhelming the target with more traffic volume than the system can handle. Like other DoS attacks, these can bring down entire websites. While not malicious, some sites have experienced similar impacts during periods of increased traffic, such as when running discounts or releasing tickets for sale.
Protocol attacks leverage vulnerabilities within specific network protocols to cause havoc. For example, SYN flood attacks overwhelm the target system with connection requests that will never be completed.
Application layer attacks exploit vulnerabilities in website attributes such as search bars and login forms. Some common forms of application layer attacks include HTTP floods, attacks in which malicious actors submit an overwhelming number of HTTP requests to a single site to paralyze the web servers handling the traffic.
What are Botnets?
To really understand DoS and DDoS attacks, you need to understand botnets.
One of the most common DoS attacks is a Distributed Denial-of-Service (DDoS) attack. (Depending on the method used, a DDoS attack can be volumetric, protocol-based, or application-layer. ) The distribution comes from using multiple devices as part of the attack, and the multiple devices are typically part of what’s known as a botnet. Botnets, short for robot networks, are collections of devices that have been hijacked by malicious actors, often without the owners ever noticing.
Botnets form and grow as attackers compromise devices by exploiting vulnerabilities on target devices and adding them to the collective botnet. They consist of three components: the bots, botmasters, and command and control servers.
Bots are compromised devices used to carry out malicious activities like DDoS attacks. Botmasters are the devices in control of the network of compromised bots. Botmasters use Command and Control servers, sometimes referred to as C&C or C2 servers, to issue commands and run scripts to get the rest of the botnet to carry out malicious activities.
Botnets are used for more than just DDoS attacks. They can be used for just about any type of cybercrime, all while providing the botmasters with a degree or two of separation from the attack. In addition to DDoS attacks, botnets are often used to carry out phishing attacks and fraud, such as generating ad revenue for websites the botmasters own.
Botnets and APTs
Advanced Persistent Threats, or APTs, use botnets to carry out malicious activities just like most malicious actors. APT attacks might be more organized than standard cyberattacks in that most cybercriminals might only be after fraudulent ad revenue or DDoS attacks.
At the same time, APTs might use multiple attack types to work toward a larger goal. For example, an APT might use a botnet to carry out a DDoS attack to generate noise and give security analysts something to respond to while also using part of the botnet to exfiltrate sensitive data slowly and more discreetly.
Impact of DoS and DDoS Attacks on IT Infrastructure
Service disruptions have massive consequences for organizations, customers, advertisers, and anyone else who relies on the site being available. Think about this hypothetical scenario: you run a website that sells about 48 items per day and hosts advertisements to add another source of income.
Assuming sales are spread evenly throughout the day, an hour of service disruption results in two lost sales. An hour of downtime might also result in lost revenue for the company that pays to advertise on your site, which could result in penalties against you depending on your contract. Service disruptions could leave your customers and advertisers with a negative view of your site, harming your company’s overall reputation.
Now, imagine that same scenario on a much larger scale. Think of how much money companies like Amazon and Microsoft could lose during even thirty minutes of downtime. Think of how many customers wouldn’t be able to do things like make purchases, access their cloud resources, play the games they’ve purchased, view the shows and movies they’ve paid for, and more. Think of how all that translates to a negative outlook on the company’s stock evaluation.
It's pretty easy to see how successful Denial-of-Service attacks can have devastating consequences.
What Strategies Can Mitigate DoS and DDoS Attacks?
Thankfully, there are ways to mitigate the risk and success of DoS attacks.
Using DDoS Protection Services
Some of these methods include using cloud-based DDoS protection services, web application firewalls, and traffic filtering. One of the major benefits of using cloud services is their ability to scale effortlessly when properly configured. Cloud-based resources can detect spikes in network traffic and scale in real-time to provide more resources to handle the uptick in traffic, effectively mitigating an attack.
Use Traffic Filtering
Traffic filtering can help mitigate DoS attacks by identifying and eliminating traffic from IP addresses with poor reputations and behavior. Rate limiting can also help reduce the number of requests devices will accept at once within a given period, which takes away an attacker’s ability to overwhelm the target resource(s).
Web Application Firewalls, or WAFs, can also help with rate limiting and traffic filtering. Load balancers also effectively mitigate DoS attacks, similar to the scalability of cloud-based protection, by evenly distributing incoming traffic among multiple resources.
Keep Programs and Software Updated
Another method of protection from DoS and DDoS attacks is maintaining a regular software patching and vulnerability remediation program. Ensuring software, protocols, and services are using the latest stable versions available helps mitigate the network’s overall attack surface, providing malicious actors with fewer opportunities.
Conclusion
Denial-of-Service (DoS and DDoS) attacks are meant to overwhelm resources and ultimately disrupt availability. When successful, DoS attacks can negatively impact an organization’s network, finances, and reputation.
There are different categories of DoS attacks, all of which aim to exploit vulnerable protocols and services by sending more traffic to a given device than it can handle. Denial-of-Service attacks can be mitigated through traffic filtering, scaling services, load balancers, rate limiting, and web application firewalls.
Learn more about things like cybersecurity, WAFs, load balancers, and packet filtering on CBTNuggets.com…just don’t make too many requests for the site at once!
delivered to your inbox.
By submitting this form you agree to receive marketing emails from CBT Nuggets and that you have read, understood and are able to consent to our privacy policy.