Networking Basics: Configuring Extended Access Lists on Cisco Routers

The Quick Definition: Access lists, also known as access control lists, are configured on routers and used to regulate traffic entering and exiting networks. Access lists can be configured for all routed network protocols such as IP.
What is an Extended Access List?
Extended Access Control Lists (ACLs) act as the gatekeeper of your network. They either permit or deny traffic based on protocol, port number, source, destination, and time range. The range of customization is massive. In this example, you'll learn to use ACLs to block a specific source from accessing a targeted computer via specific ports.
How to Set Up an ACL
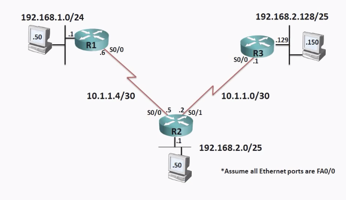
Imagine a computer (192.168.1.50 in the illustration) attempting unauthorized access of 192.168.2.50 via HTTP and HTTPS — and you want to stop that activity.
You don't want to stop all traffic between these two IP addresses. That will cause a network outage. Instead, you want to restrict traffic only between the ports. HTTP is port 80. HTTPS is port 443.
The first thing you want to do is define the source IP address, which in this case is the unauthorized 192.168.1.50. You'll first want to block all traffic from that IP address, which you can do with a wildcard mask, which acts as the filter within that source subgroup.
You can read all about how wildcard masks work in another post. In this example, you should know that entering 0.0.0.0 here will block every octet of the IP address. In this case, that would deny every access attempt from the 192.168.1 subnet. The illustrated example above only has one host, though. If you enter "host", there's no mask request, and instead asks for a destination.
Setting the Destination
Now that the target is identified, it's time to input the restricted destination. In its current form, this ACL will deny all TCP traffic between 192.168.1.50 and 192.168.2.50. But you don't want to do that. This is where the port-specific functionality becomes important.
With these statements, you'll deny the ports access to your network.
Router1# conf t
Router1(config)# access-list 150 deny tcp host 192.168.1.15 host 192.168.2.50 eq 80
Router1(config)# access-list 150 deny tcp host 192.168.1.15 host 192.168.2.50 eq 443
The first statement blocks the target at port 80 of the destination. The second statement repeats the process for HTTPS, which is port 443. The keyword "EQ", meaning equal to, will allow for entry of specific ports.
To check the list, call up the list ("Show Access List"), which will return the two new statements.
Router1(config)#do sh access-list 150
Extended IP access list 150
10 deny tcp host 192.168.1.50 host 192.168.2.50 eq www
20 deny tcp host 192.168.1.50 host 192.168.2.50 eq 443
The first denies the first host from connecting with the second using port 80 (HTTP) and the second statement denies the same using port 443 (HTTPS). The ACL now includes the necessary instructions. But the configuration isn't over, yet, and is not ready to be applied to an interface.
Negating the "Deny All"
At the end of every ACL, there is an 'Implicit DENY ALL' statement. This statement does not show up in the configuration or when you run the 'show access-list' command. But, it is ALWAYS there. " So, if you only add the two deny statements covered above, that implicit deny statement will block all access and cause a total network outage. To fix this, the ACL needs a permit statement, as well.
Bring up Access List 150 (the number assigned to this list) and add "Permit". Configure the permit to include IP from any source to any destination address. By allowing all variations within the statement, the "deny all" function is overruled and no longer causes that outage. Instead, only the two deny statements you created will now apply, and all other traffic will now be permitted.
Router1(config)#access-list 150 permit ip any any
Router1(config)#do sh access-list 150
Extended IP access list 150
10 deny tcp host 192.168.1.50 host 192.168.2.50 eq www
20 deny tcp host 192.168.1.50 host 192.168.2.50 eq 443
30 permit ip any any
Applying the ACL and Determining Direction
Cisco best practices indicate that this list should be applied as early in the sequence as possible. In this case, that's at Router 1. In the console, enter "int fa0/0" for the FastEthernet 0/0 interface and then the command "ip access-group". Then enter the relevant list number, which in this case is 150.
The console will then query "in" (inbound package) or "out" (outbound package), which requires determining the direction. The best possible advice here: be the router. Imagine each of your arms is an interface, one FastEthernet 0/0 and one serial 0/0, and ask which direction the traffic is coming from. In this case, the traffic is coming in the interface, which in this example indicates that the final entry of applying the access list should be "in".
Router1(config)# int fa0/0
Router1(config-if)#ip access-group 150 in
With the access list applied, host 192.168.1.50 will no longer be able to reach host 192.168.2.50 using either port 80 or 443, and your work is done!
CBT Nuggets ACL Courses
Learning networking technologies for the first time can seem like a daunting task. From subnetting to spanning trees, there is a lot to study and understand. Our CCNA training lays it all out for the new network professional.
Want to learn more about access lists on Cisco routers? Here's Jeremy with more on the topic!
delivered to your inbox.
By submitting this form you agree to receive marketing emails from CBT Nuggets and that you have read, understood and are able to consent to our privacy policy.