Getting Started with CBT Nuggets AWS Labs Tools

I love to eat at buffets. Deep down, I am a consumer and enjoy having things managed and prepared for me, and I think it's one of the reasons why I love cloud computing. Then again, like being billed for hidden service fees, nothing stings worse than returning to the table after a trip to the buffet only to receive the bill and find out the dessert bar and champagne service were extra. Womp womp.
Getting started in IT often means a lot of lab time, experimentation, and a sure-fire sprinkling of gotchas. But, as they say, you have to learn to walk before you can run. At CBT Nuggets, we want that experience to be as productive and lucrative for learners as possible. In fact, so much that I created free AWS Lab Tools training to help you get hands-on with the AWS platform. This quick 6-video training walks you through how to set up an AWS account, so you can start learning how to use AWS and its services.
What are AWS Labs Tools from CBT Nuggets?
What exactly are AWS Labs Tools? In short, it is a CloudFormation template, which installs and configures your AWS account for you. An admin/developer like myself can write these templates and have AWS follow the instructions, drastically simplifying the "deployment" process for learners like yourself. More specifically, the template creates the following:
A limited permissions lab user
Only the most common AWS Associate-level services
Single-region limit
Simplified permissions management
Free-tier limits
t2.nano, t2.micro, t3.nano, and t3.micro EC2 instances
standard & gp2 EBS volumes up to 15GB
db.t2.micro RDS instances
Email-based billing alerts (optional)
AWS command line and development environment
Non-Default VPC, with public and private subnets
Sounds pretty good right? At a high level, the deployment process involves a handful of simple steps:
Sign up for a new AWS account (credit card required)
Manual configuration steps
Set an alias for your AWS account
Enable billing alerts
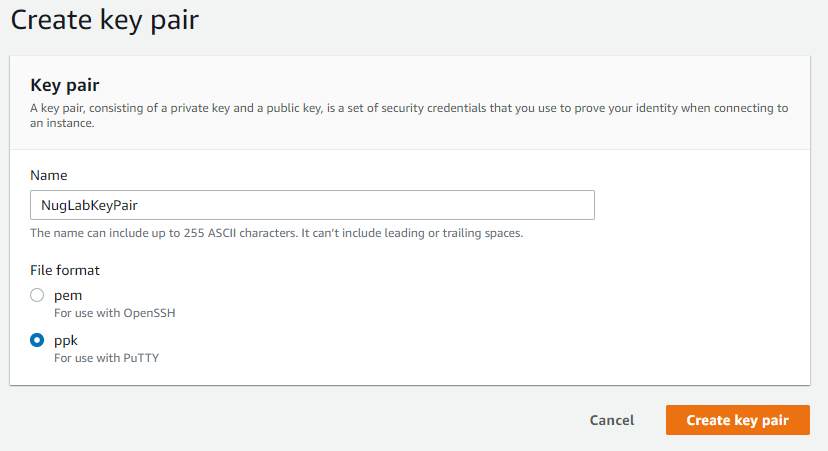
Create an EC2 Key Pair
Deploy CBT Nuggets AWS Labs Tools CloudFormation template
Run AWS CLI configuration script (provided)
Ready? Let's get this deployed.
Step 1: Build a New AWS Account
Head over to https://portal.aws.amazon.com/billing/signup and follow the on screen prompts to get your new AWS account created.
When setting the AWS Account Name, be sure to choose something unique, descriptive, and easy-to-remember. This name is known as your account alias and provides a human-friendly identifier as an alternate to the numeric number that AWS assigns.
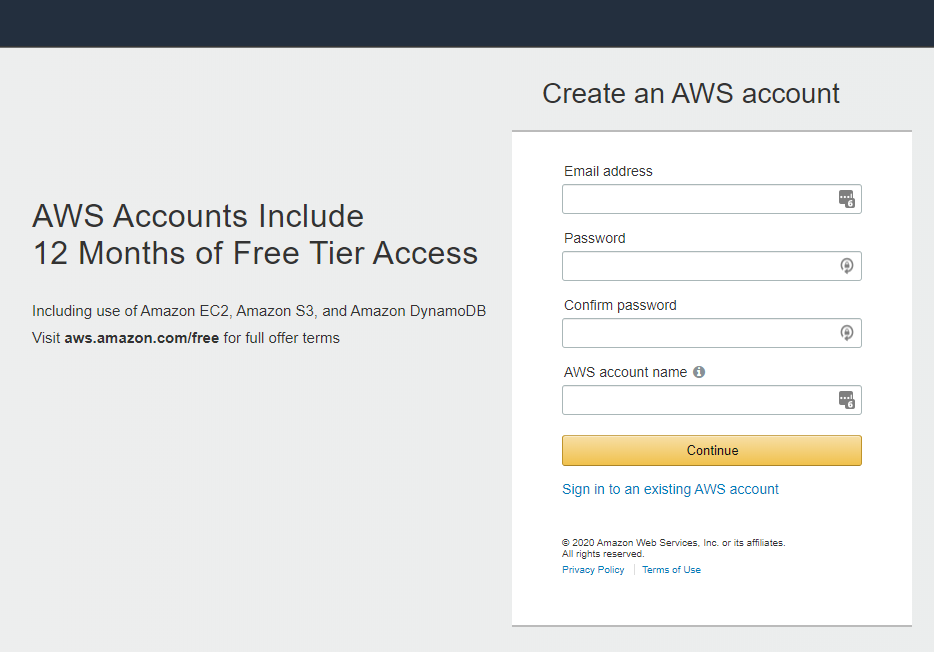
For more info, AWS provides a great step-by-step guide for initial account creation.
Step 2: Configure First Time Account Settings
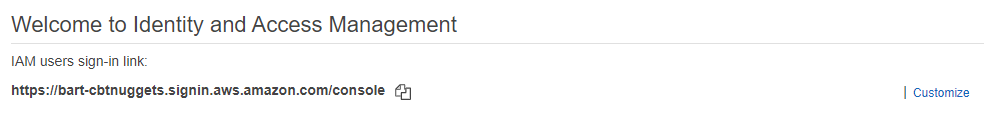
Set/Confirm Account Alias. Browse over to IAM Home and make sure you see a lovely IAM users sign-in link: shown at the top — if this URL contains a string of number (your account number) then take a moment to use the on-page link to a set a new account alias name. When finished make a note of this alias and the sign-in link
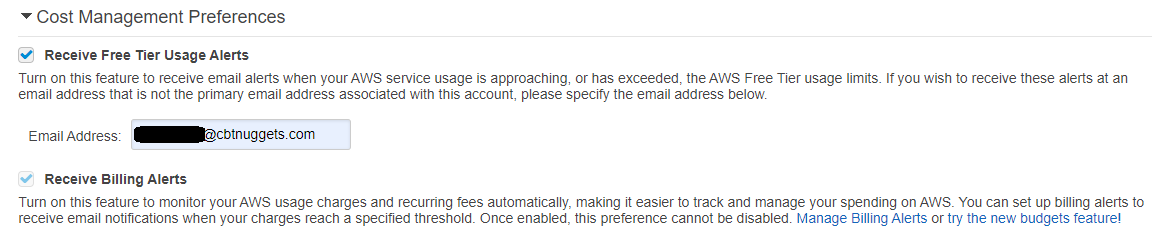
Set/Confirm Cost Alerts. Browse over to Billing and make sure that you have Receive Free Tier Usage Alerts checked/enabled, and specify a preferred email address. Also, ensure that Receive Billing Alerts has been checked/enabled.
Create EC2 Key Pair. Browse over to the EC2 Key Pair dashboard and make sure that you have created and downloaded an EC2 key pair (make sure you know where you stored the key). If not, create a new key pair, making sure to provide a descriptive name and note where you save the downloaded key file (.pem for Mac/Linux or .ppk to use with PuTTY on Windows)
Step 3: Deploy AWS Labs Tools Template
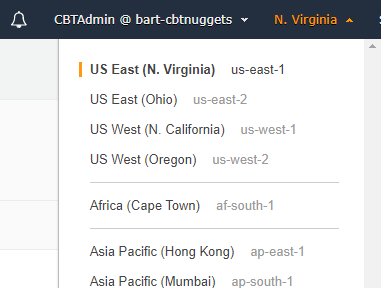
While still logged into the management console, switch to the region you plan to use most often (typically the one closest to where you live/work).
Once you have confirmed you are in your preferred region, browse over to the following CloudFormation Quick-Create link.
This should land you on the Quick Create Stack page, where you can see the Stack Name has been pre-populated for you. Feel free to change the name or leave it as is.
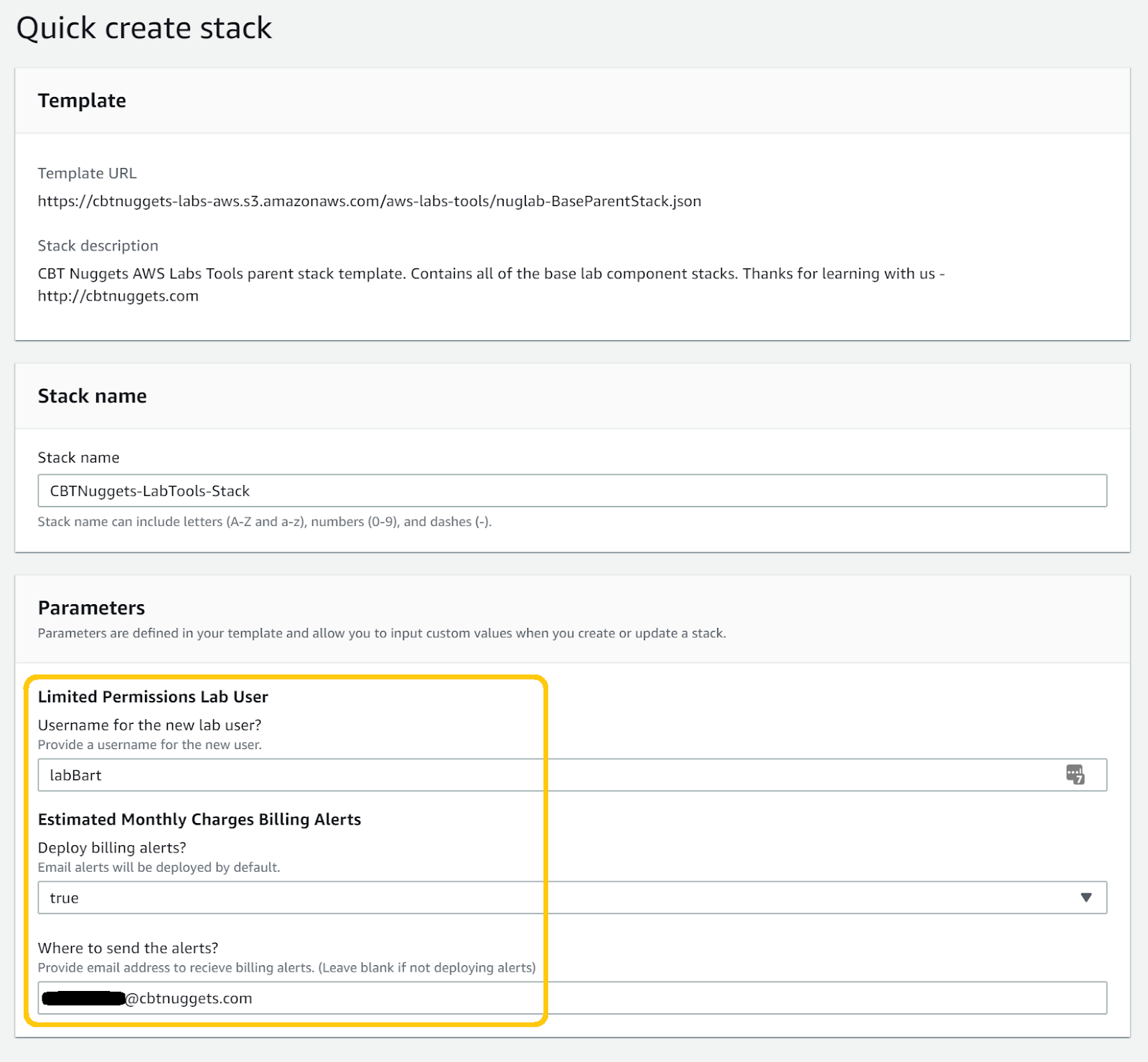
Enter a preferred username for the limited permissions administrator account.
Select true/false to deploy the email billing alerts (optional).
Enter your preferred email address if deploying the billing alerts (we suggest using the same email as the free tier alerts from earlier).
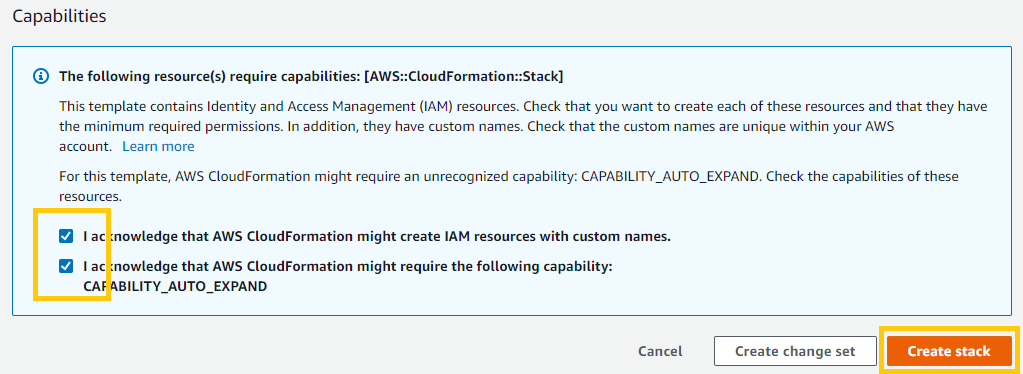
Scroll to the bottom of the Quick create stack page and check both of the Capabilities options. These are required to allow CloudFormation to create users and security policies, as well as create other CloudFormation stacks (contained within the template). When ready click [Create stack].
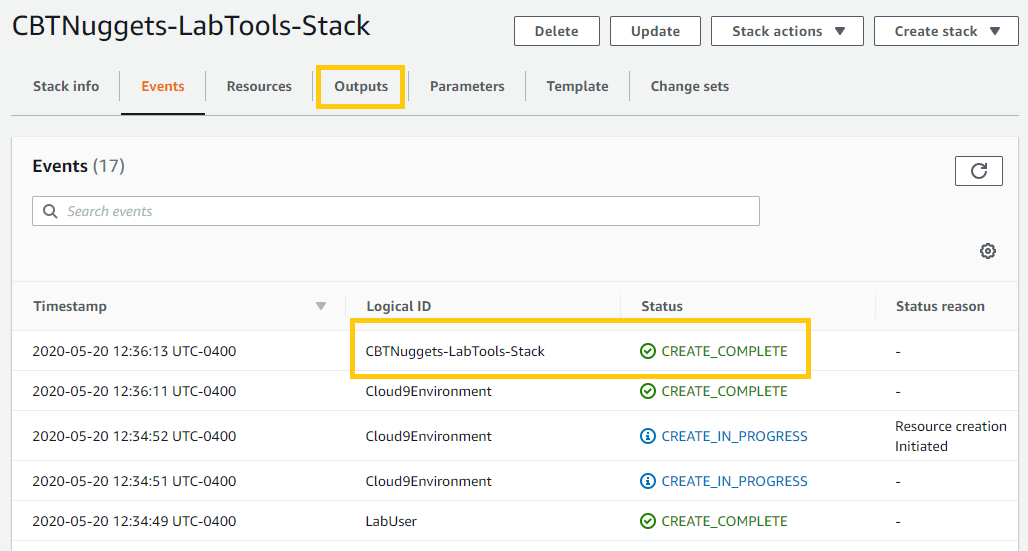
On the following page you should see deployment status information. You can refresh the list of events and follow along as CloudFormation unpacks the tools templates and creates your new resources. The lab templates make use of what are known as "nested" CloudFormation templates. You will see these "other" templates being created for you as you follow along.
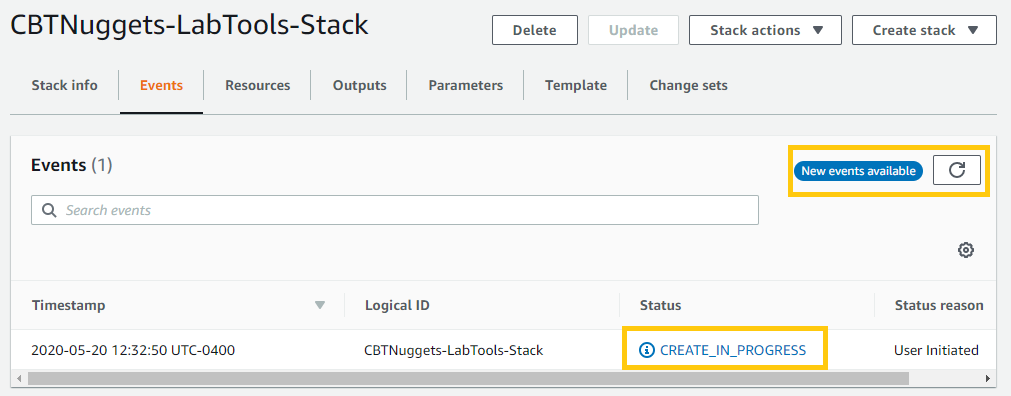
Refresh the events list until you see the CREATE_COMPLETE event for the CBTNuggets-LabTools-Stack. Once finished, locate and click on the Outputs tab above the stack events list.
On the lower section of the page you will find important details about what the template has created for you.
Lab user's username
Lab user's access key
Lab user's secret access key
Cloud9 Environment URL
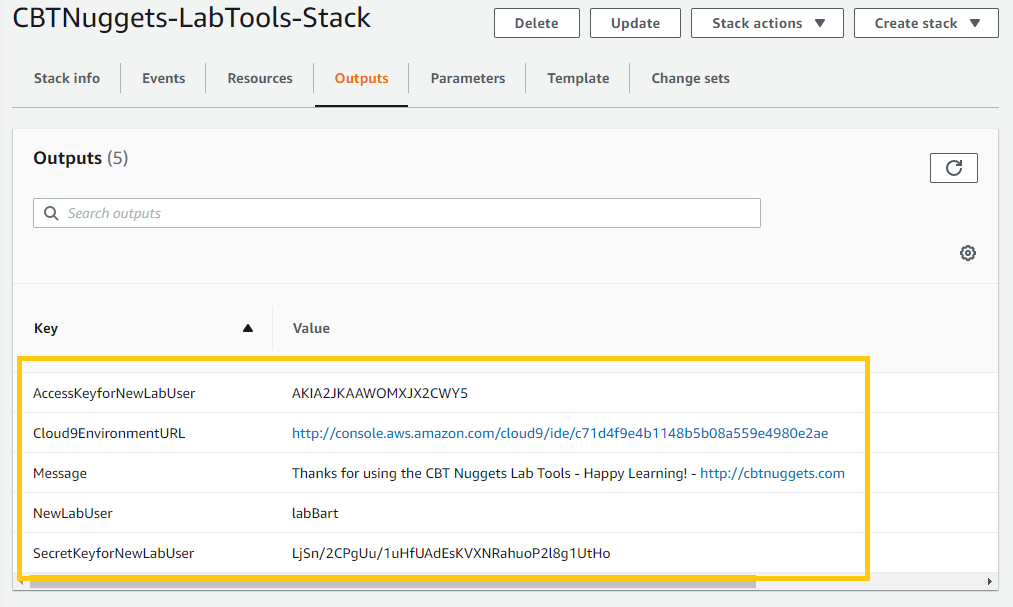
* Make a note of these items for later use *
Step 4: Test and Finish
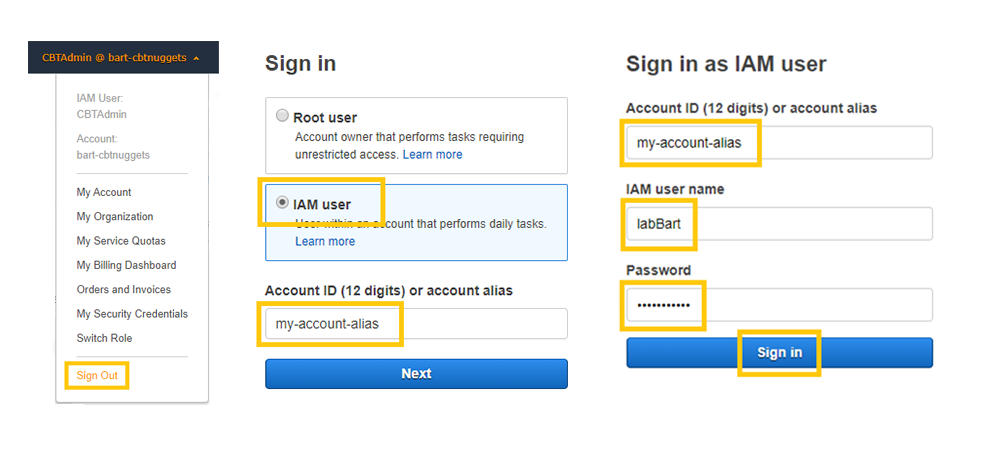
Now that your new lab user has been created, it's time to log your current user out of the management console and log back in using the new lab user. Once logged out, you can browse over to your account's Sign-in Link from earlier or head over to http://console.aws.amazon.com and choose the [IAM User] option and enter your Account Alias from earlier, then click [Next].
On the Sign in as IAM user page confirm your account alias, enter your new lab user's username from earlier and then enter the default password: Cbtnuggets1!
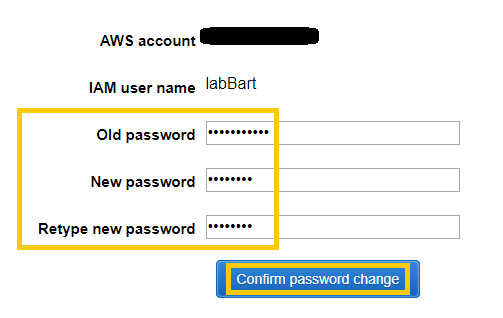
Take a moment to change the lab user's password. The new password will need to meet AWS' complexity requirements (see below). Make a note of this new password in a secure location.
Password Complexity:
Must contain at least 8 characters
Must include a minimum of three of the following mix of character types: uppercase, lowercase, numbers, and ! @ # $ % ^ & * ( ) _ + – = [ ] { } | '
Click [Confirm password change] to be taken into the management console with your new lab user account.
Double-check that you are still in the correct region from earlier. Remember, by design this new user can only work in the one configured region.
We're almost done!
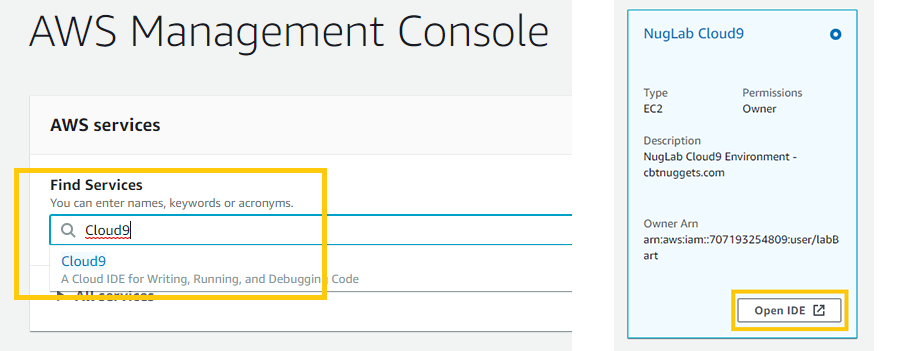
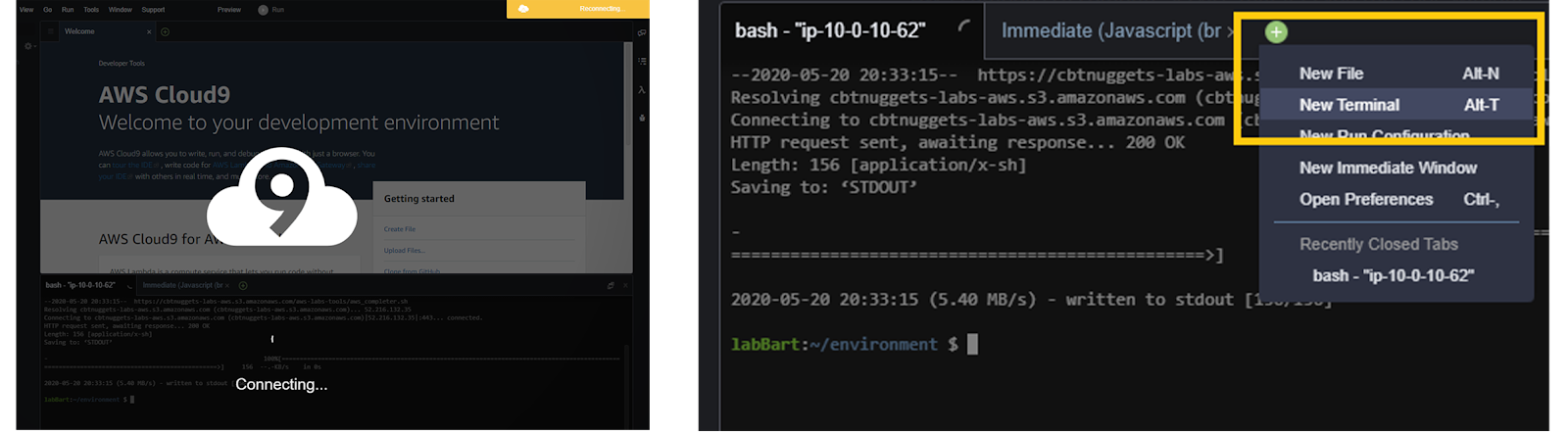
The final configuration of the CBT Nuggets AWS Labs Tools is to configure the AWS Command Line over in your new Cloud9 environment. While still logged in, locate and browse over to the Cloud9 Environment URL from earlier, or use the services drop down window and enter in Cloud9 to access the Cloud9 service dashboard, click on the [Open IDE] launch link for the NugLab Cloud9 environment.
Locate the Terminal window pane, labeled with bash – "ip-10-0-10-xx" or something similar. This is your AWS Command Line, running on an EC2 instance (managed by Cloud9).
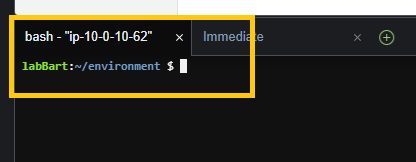
Configuration is completed by running updates and configuring command-completion.
In the terminal, paste in the following command and press [Enter] (You can drag the window panels to resize).
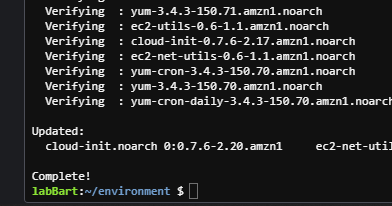
sudo yum update -yYou should see packages download, install, and then verify. Look for the Complete! to know it has finished.
Next, in the terminal, paste (see note below first) in the following command and press [Enter].
sudo wget -O – https://cbtnuggets-labs-aws.s3.amazonaws.com/aws-labs-tools/aws_completer.sh | bashNOTE: You'll need to replace the red en-dash above with a hyphen.
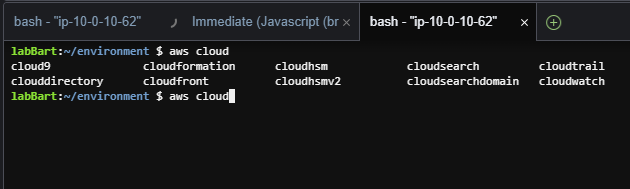
The Cloud9 interface should freeze while your instance reboots. After a minute or two, open a new terminal window by clicking on the [+] and choosing New Terminal. You should once again see the :~/environment prompt.
AWS CLI command-completion is now configured on this EC2 instance and ready to help you out! To test it you can try typing in aws cloud and then hit the [Tab] [Tab] on your keyboard (twice). You should see it return a series of commands that complete what you have typed so far. Voila!
Now that you have the tools deployed and your command-completion configured, you are ready for some serious AWS learning and labbing. A few things to keep in mind:
You need to use your new lab user for the limited permissions to work.
Keep an eye out for any billing alerts you may receive and follow up on unknown/unexpected charges.
If you chose not to deploy the billing alerts, then consider configuring some manually.
You can always create new users or modify the permissions of the lab user by browsing over to https://console.aws.amazon.com/iam and making changes through the management console. In particular look for the NugLabLimitedGroup and you'll find the lab user, as well as the two permissions policies that control the lab user's permissions.
You can always go back to the CloudFormation dashboard, locate this CBTNuggets-LabTools-Stack, and then [Delete] it, removing everything that was created for you.
As with all things in the world of learning, this is just a starting point. Eventually, I'm sure you will find yourself well equipped to protect your own accounts — and those of your employers and business partners.
Feel free to browse through these templates and use them to learn about the power of Infrastructure-As-Code, CloudFormation, and AWS Cloud best practices. Check back here for future announcements regarding template updates, related training material, and more AWS Cloud best practices from the team here at CBT Nuggets.
And again, if you found this post helpful, check out my free AWS Lab Tools training here at CBT Nuggets. Together, we'll get you set up with an AWS account so that you can start learning how to use this versatile platform!
delivered to your inbox.
By submitting this form you agree to receive marketing emails from CBT Nuggets and that you have read, understood and are able to consent to our privacy policy.